The Great AI Adapter Race: Why Your Product's Next Superpower Is a Humble MCP Server
First things first: This blog/article is not about the usage of MCPs from coding tools like Claude Code. The effectiveness of MCPs in that coding tool context is questionable at this point due to the availability of CLI tools which are proving to be a lot more context and token-friendly. This blog is about usage of MCPs in the context of Agentic workflow development.
With that out of the way, let’s begin.
Most teams I talk to are doing the same thing right now.
They are wiring Agentic Workflows and LLMs into products. Fast. Sometimes a little too fast. These Agents can do stuff, and they need tools. You need to wire the right tools to the agents.
And the wiring job looks familiar: custom connectors, one-off tool calls, brittle prompt glue, and a growing pile of code nobody wants to touch six months from now. I’ve seen it all before. First with integrations and APIs trying to cram everything into a ‘simple’ interface and dealing with the consequences. And with identity and access management and having to juggle all the different flavors of the same concept. The first version ships, and everything seems amazing. Then the second version arrives, and the pain begins.
Want less Noise, more silence? The Model Context Protocol (MCP) is a quieter shift that I believe will actually stick. One way to think about MCP is as a “USB-C port for AI systems.” Think about the usability improvements that came with moving from older USB connectors to a single, smaller USB-C on both host machines and devices. Suddenly you had a single port that you could use with all sorts of different devices that didn’t have to change or think about what cable or adapter to bring along. Probably similar usability benefits will come from having a single protocol for describing what each model is about, so to speak. One port. Many devices. Less hassle.
This piece is my perspective, pure and simple. It gathers up everything I’ve seen in the MCP world, showcasing what I honestly think makes a difference. But hold on, there’s more. One thing, people just don't seem to properly value: security.
Subscribe (button at top right) to get these blogs in your inbox, and enjoy additional features!
Summary
MCP turns AI integrations from custom wiring into a repeatable, swappable contract, but the contract is only as safe as your auth.
Everyone’s in a mad scramble to add AI features in their product. In the excitement of adding AI to whatever they’re working on, the typical response has been to roll their own connector to a third party system or API of their choice. That model works just fine until it doesn’t.
MCP is an emerging standard that provides structure over the chaos and describes a neat way that an AI client can make use of new tools through lightweight adaptation servers. Having a plugin architecture for assistants, and the ability to quickly develop new features, and the need to implement relatively few changes when models evolve, are all characteristics of MCP-based systems.
A big upside? Absolutely. The danger, though? Just as real. Seriously, if a public MCP server goes live without any truly robust authentication, you can bet your bottom dollar it's going to act like a giant, flashing neon sign, attracting the exact type of trouble that forces security folks to throw their hands up in pure frustration and scream, "Didn't we just say this would happen?" A real mess. I will lay out the good stuff, and the bad stuff too. Then, what I think is coming.
Introduction: From Tangled Wires to a Universal Outlet
If every API/system needs a custom integration, you do not have a product strategy, you have a maintenance strategy.
Remember the drawer full of proprietary chargers?
This is what early AI integration feels like in a lot of product organizations. Every new internal feature, every third party API all require some new adapter. It’s not a big deal at first but after a while nobody can tell you what tools the assistant can call in production and who approved them.
So, MCP? What's that? It is a protocol. Totally open, too. The big picture's pretty straightforward: AI assistants, they simply gotta use outside tools. Not through some crazy zoo of custom-built rigs, you get me? Instead, there just has to be one single interface. Easy to find, completely unified. Just one. Imagine that!
If that sounds boring, good. Boring is where scale lives.
Here is what I want to unpack:
- What MCP actually is, in plain engineering terms
- Why adoption is picking up
- What it changes for developer experience and user experience
- The security and governance issues that can bite you hard
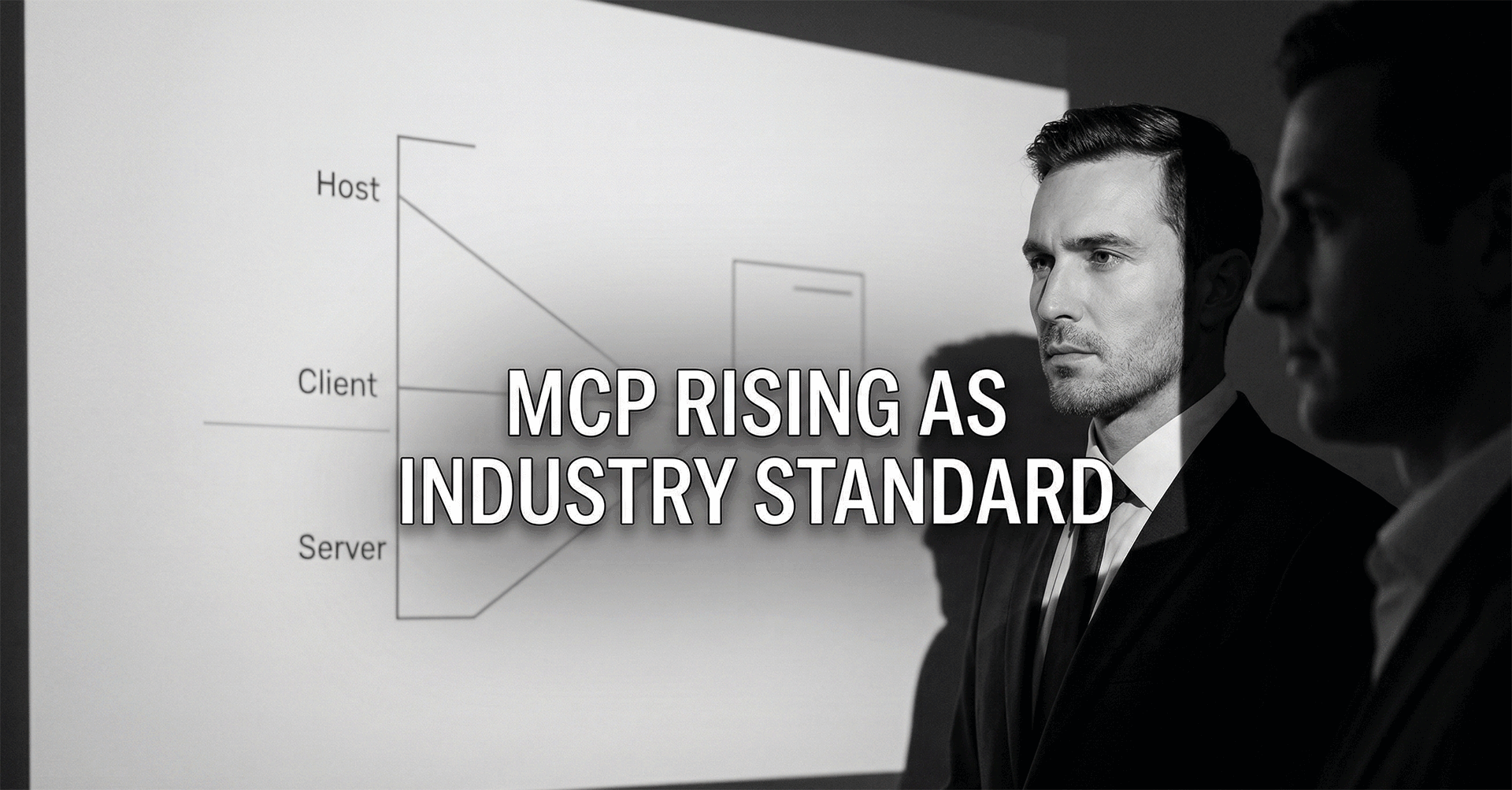
The Tipping Point: From Niche Protocol to Industry Standard
Standards win when the cost of doing nothing becomes higher than the cost of changing.
MCP is an integration standard that draws a clean line between three layers:
- The Host UI: Where the user interacts
- The AI Client: The model runtime that decides what to do
- The MCP Server (Adapter): A thin wrapper that exposes a capability as a standardized tool
That third piece is the workhorse. The MCP server is where your thing becomes a device an assistant can find and use.
This is not a thought experiment anymore. Everyone is discussing about MCP for business workflows around sales, e-commerce and even fintech. The category does not matter as much as the pattern – which is that teams need access to tools that are the same across different models and instances of assistants.
The Developer Experience: LEGO Bricks for AI Tooling

The best developer experience is the one that stops you from inventing a new pattern every sprint.
When MCP clicks, it feels like LEGO.
Not because it is cute. Because you stop rebuilding the car.
Why spread your tools' 'brains' all over your application, then shove 'em into every single prompt? This clever adapter, it is the pivot point. The server just does the talking. Your main product stays so much tidier. You are not forced to redo half of your integration setup simply because a tool switch is desired. With so many diverse tools and models appearing, that's a huge deal.
Tooling is moving quickly, and it is not evenly distributed across stacks:
- In Python, FastMCP lowers the friction to stand up a server fast.
- In .NET, the community is filling gaps with collections like MCPP.NET via Awesome-DotNET-MCP, which helps teams wrap existing OpenAPI specs and legacy services.
Java development is moving quickly to embrace these standards as well. To avoid the friction of custom integration code, the community is coalescing around adapters found in repositories like punkpeye/awesome-mcp-devtools on GitHub:
- quarkus-mcp-server: Bridges the Quarkus framework to MCP, allowing teams to stand up standardized tool servers without rebuilding the plumbing.
- spring-ai-mcp: Delivers the foundational Java SDK and integration patterns required for the Spring ecosystem.
- tinystruct-mcp: A lightweight SDK designed for crafting extensible MCP servers using the tinystruct framework.
That ease is a gift. It is also how you end up with "shadow tools" in production if you are not careful. Which brings us to the part everyone wants to skip.
The Elephant in the Room: Security, Governance, and the Authentication Challenge

If an agent can call tools, attackers will try to call your tools through the agent.
If you build MCP servers and choose to make them public facing, then authentication was discussed in the very first design meeting.
Why? Your threat model just changed. You’re no longer just protecting an API endpoint. You’re protecting an endpoint that could be called by an AI client after it has received user input. And let’s be real, you know all the crazy things users will input into any system. And tool poisoning and unauthorized access are not a joke if you treat your tool layer like a demo.
The teams that win here will do something unglamorous: they will make tool access boring, audited, and tightly scoped.
A few providers are leaning into MCP auth patterns already:
- Auth0: Strong fit for enterprise-grade auth, MFA, SSO, and fine-grained RBAC.
- WorkOS: Great for B2B SaaS teams that need SAML/SCIM and quick enterprise IdP hookups.
- Cloudflare Access: Useful if you want Zero Trust controls at the edge, often with minimal app changes.
I've got a simple rule. Seriously. When folks first start talking about that MCP project, if it is all about those 'cool demos' – the flashy bells and whistles, you know – and not about who actually can do what, those boundaries for authorization, or the actual permission schemes... look, you're just asking for colossal trouble. A seriously painful post-mortem later? That absolutely will happen. Don't doubt it.
From Backend Plumbing to Brilliant UX
The user does not care about your protocol, they care that the assistant finally does something useful.
Nobody buys Agents. They buy outcomes. And to provide that outcome, MCP is huge. Seriously, it's a game-changer. Think about what we can accomplish right there, in front of users. Those frustrating, dead-end chat boxes, the ones that just spit out answers but never actually do anything inside your product? You can forget about them. We're tired of 'em.
A few early UX patterns are worth watching:
- Figma's Dev Mode: Pulling tokens, components, and layout context through an MCP server to improve design-to-code accuracy. That workflow has been broken for years. If MCP helps close the gap, developers will notice.
- Contextual sidebars in tools: An assistant in an IDE that quietly pulls relevant internal docs while you code, using something like an Outline-style MCP server.
- Structured outputs rendered as UI: Instead of walls of text, tools return structured data and your UI renders widgets like charts, drafts, and previews.
We do not have a ton of public, hard metrics yet. That is normal early on.
The direction is still obvious: MCP makes "context-aware" stop being a marketing word and start being an engineering capability.
Synthesis of Insights and Key Conclusions
MCP is not magic, it is leverage, and leverage always comes with a bigger blast radius.
After experiencing the ecosystem and developing a few implementations, a few things stand out:
- MCP looks sticky. When engineers taste standardized tool integration, it is hard to go back to custom glue code.
- Speed vs. security is the real trade. MCP can increase development velocity, but insecure tool layers can turn that velocity into incident response.
- UX is the prize. Cleaner integrations are nice. Experiences that actually help users finish work are what move revenue and retention.
- There is room for leaders. Best practices are still forming. Teams that build discipline early can shape internal standards, influence open source, and create defensible product behaviors.
Implications and Future Directions
The next platform battle is not model quality, it is who controls context safely.
Two things I expect to see become more important:
- Not fooling around with context engineering as a “concept” but actual context engineering as a profession. The difference between doing a quick assessment and actually designing the information flow for the rest of the application.
- Choosing what tools will be used, what data will be available to those tools, how that data will be represented and how the application will be monitored.
And then there will be performance and operability concerns. For all the apps that will use MCPs: latency, observability, retries, and debugging are all still important issues. Agents, MCPs, and Tool calls need to be as traceable as anything else happening in production.
I think we will also quickly see the appearance of MCP native security and monitoring tools, because the needs are evident and the motivations for meeting them are high.
If you’re like me and you have a team of engineers and face decisions about which tools to buy, my recommendation is not to “bet the farm.” Rather, consider running a small trial with a small number of valuable tools, behind a secure login with trusted logging and a known rollback path.
Then learn.
Conclusion
The teams that treat MCP like infrastructure will outpace the teams that treat it like a demo.
MCP is about the connection between the model and the physical system. Really about simplifying the work to get there. Less wire chasing. More standardized interfaces. Faster feedback loops as the models evolve.
Smart products sound great to our customers, suppliers, and especially to sales teams. But it is a double edged sword. The adapter which is needed in order to enable smart functionality may also turn the product to be a brand new attack vector for IT people, a brand new source of governance issues for regulatory people and a huge amount of unpleasant surprises to all production staff if it is not designed with the utmost of care and respect to all challenges involved.
The AI adapter race is on.
Just stacking up a bunch of software? That isn't how anybody triumphs. Nope. Real winners, they are the teams truly capable of pushing out capabilities that are both genuinely useful and absolutely secure, all while keeping them properly governed. This happens without letting their foundational architecture melt down into some chaotic, unholy tangle.


Comments ()